How to Fix the WordPress “Sorry, You Are Not Allowed to Access This Page” Error
February 9, 2026
How To Reorder Pages In WordPress Easily
February 10, 2026You're editing a post in wp-admin, hit save, and WordPress kicks you out. "Your session has expired. Please log in again." It's one of the most common WordPress login problems, and it almost always comes down to authentication cookies failing to validate.
The good news? It's fixable. Usually in under five minutes.
This guide covers how to fix the WordPress session expired error, from clearing browser cookies and resetting security keys in wp-config.php to fixing URL mismatches, SSL issues, plugin conflicts, and server-side caching. Each method targets a specific cause so you can skip straight to the one that matches your situation.
What Is the WordPress Session Expired Error
You're halfway through editing a post in wp-admin, and then it hits. "Your session has expired. Please log in again." The page refreshes. Your changes? Gone.
This is the WordPress session expired error, and it's one of the most common login problems on the platform. WordPress powers roughly 43% of all websites on the internet, according to W3Techs. That's over 500 million sites. A good chunk of those site owners have stared at this exact message at least once.
The error appears on the wp-login.php screen. It shows up when WordPress can't validate the authentication cookie stored in your browser. That's it. The session didn't actually "expire" in the traditional sense, not like a PHP session timing out on the server. WordPress doesn't even use PHP sessions for login.
Instead, WordPress relies entirely on browser cookies for authentication. Two cookies, specifically:
- wordpress[hash] stores your login details and only works inside the /wp-admin/ area
- wordpressloggedin[hash] tells WordPress who you are across the rest of the site
If either cookie fails validation, WordPress boots you out. The error typically appears when you're saving a post, accessing the admin dashboard, or trying to log in and getting stuck in a redirect loop.
Worth knowing: this is different from being logged out because you were idle for too long. The default cookie lifetime is 48 hours without checking "Remember Me," or 14 days with it checked. The session expired error happens when the cookie itself is corrupted, blocked, or mismatched, not when time runs out.
Why WordPress Login Cookies Fail
The cookie validation process in WordPress is surprisingly strict. The wpvalidateauthcookie() function checks the username, expiration timestamp, session token, and an HMAC hash on every single request. If any piece is off, you're out.
Patchstack's 2025 security report found 7,966 new vulnerabilities in the WordPress ecosystem during 2024, a 34% jump from the year before. While most of these target plugins, the same ecosystem complexity that creates security holes also creates cookie and session problems.
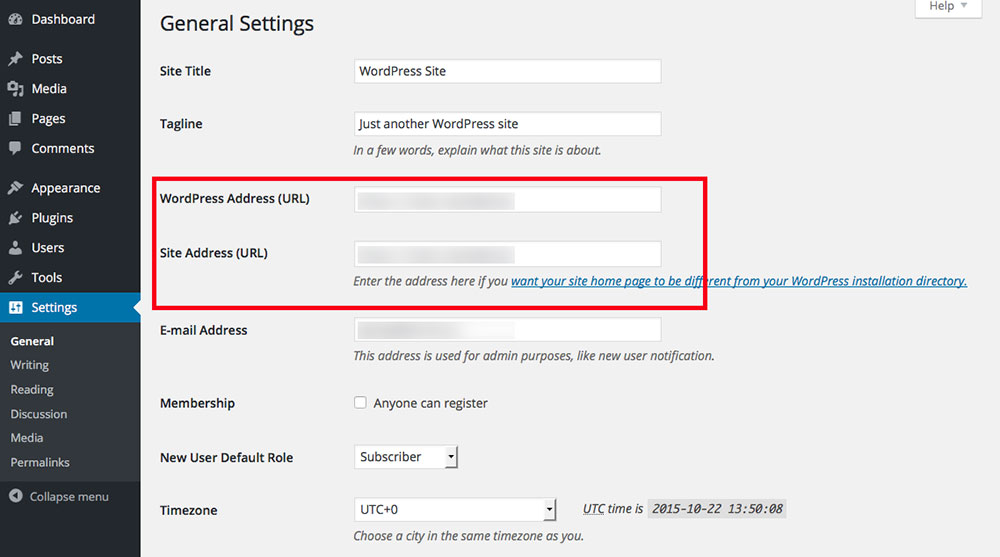
WordPress Address vs. Site Address Mismatch
This is the number one cause. Your mileage may vary, but I've seen this trip up more people than anything else.
WordPress stores two URLs in the database: WordPress Address (URL) and Site Address (URL), both found under Settings > General. The authentication cookie is hashed using the site URL. If those two values don't match exactly, the cookie hash won't validate.
Common ways they get out of sync:
- One uses
www.and the other doesn't - One uses
https://while the other still sayshttp:// - A migration or domain change updated one but not the other
Even a trailing slash difference can cause it. WordPress is that picky about URL matching.
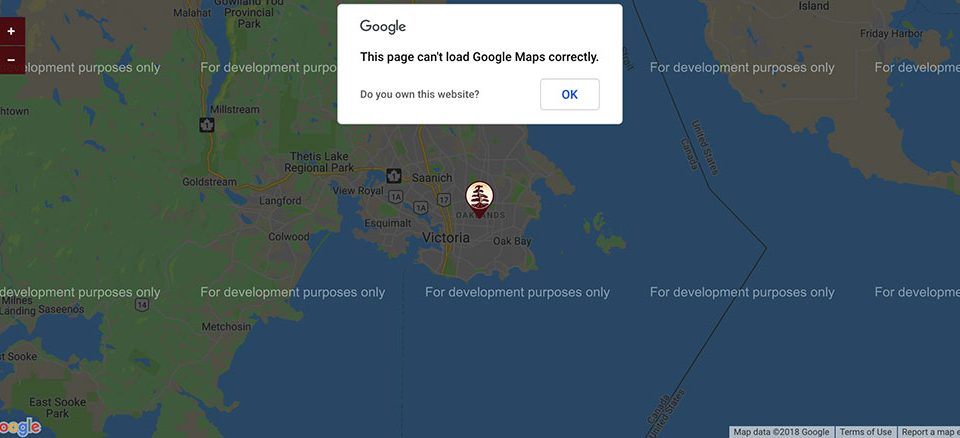
Mixed Content and SSL Certificate Problems
SSL issues cause the session expired error more often than people expect. If your certificate is expired, misconfigured, or only partially applied, the browser may refuse to send the authentication cookie over what it considers an insecure connection.
Mixed content is the sneaky version of this. Your site loads over HTTPS, but some resources (images, scripts, login form actions) still point to HTTP. The browser flags this, cookies get blocked or downgraded, and WordPress can't authenticate you.
A critical vulnerability (CVE-2024-10924) in the Really Simple SSL plugin, which affected over 4 million WordPress sites, showed just how fragile SSL-dependent authentication can be when plugins handle it poorly. Wordfence reported the flaw with a CVSS score of 9.8.
Clear Browser Cookies and Cache
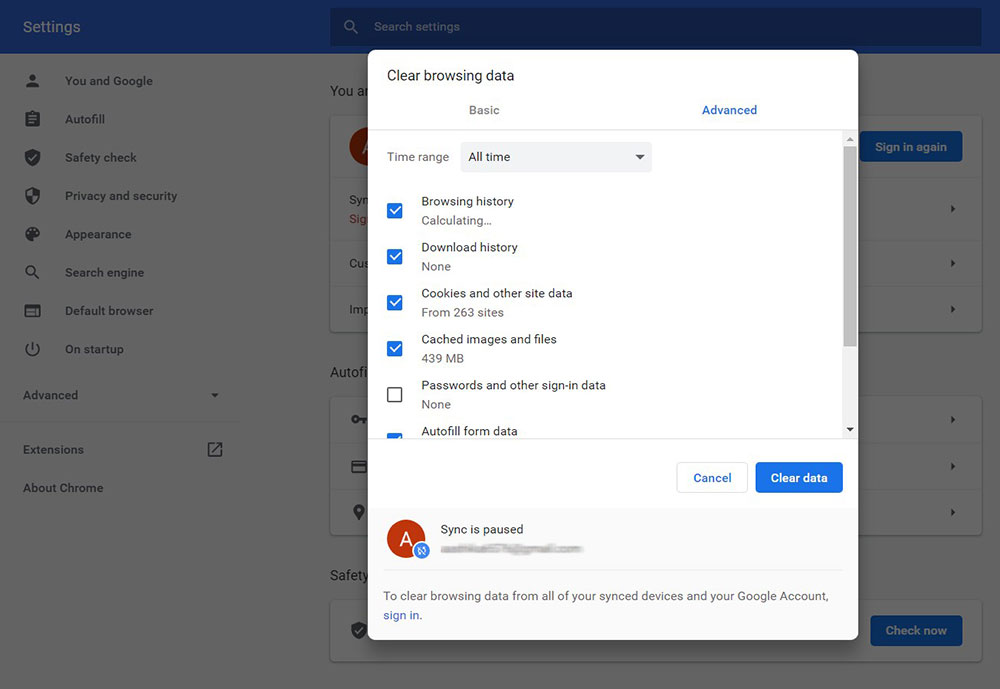
Try this first. Seriously. It fixes the problem for most people and takes about 30 seconds.
Your browser might be holding onto an old, expired authentication cookie from a previous session. WordPress sees the stale cookie, tries to validate it, fails, and throws the session expired message. Clearing that cookie forces a fresh login with a new, valid cookie.
The targeted approach (better than nuking everything):
- In Chrome, click the lock icon next to your site URL, then "Cookies and site data," and remove only your domain's cookies
- In Firefox, go to Settings > Privacy & Security > Manage Data, search for your domain, and remove those entries
- Safari users can go to Settings > Privacy > Manage Website Data and search for the specific domain
Before you clear anything, though, test in an incognito or private browsing window first. If the login works fine in incognito mode, you've confirmed it's a browser cookie issue. No need to guess.
Check your browser extensions too. Ad blockers, privacy tools like uBlock Origin or Privacy Badger, and even some antivirus browser extensions can block or modify cookies. I've personally spent an embarrassing amount of time troubleshooting a login loop that turned out to be a browser extension silently eating cookies.
Plugin conflicts account for 65% of technical malfunctions reported on WordPress sites in 2025, according to Digidop research. But before you start deactivating plugins on your server, rule out the browser side. It's faster and less risky.
Force Fresh Cookies in wp-config.php
When clearing browser cookies doesn't work, the problem might be on the server side. Specifically, the secret keys and salts that WordPress uses to hash your authentication cookies.
WordPress stores eight cryptographic constants in your wp-config.php file:
| Constant | Purpose |
| AUTH_KEY | Signs cookies for admin area access. |
| SECURE_AUTH_KEY | Signs cookies specifically when SSL is active. |
| LOGGED_IN_KEY | Signs the logged-in cookie used site-wide. |
| NONCE_KEY | Protects form submissions and URLs from misuse. |
| AUTH_SALT, SECURE_AUTH_SALT, etc. | Adds extra randomness to each key's hash. |
These values are baked into every authentication cookie hash. If they're blank (some cheap hosting setups leave them empty), compromised, or identical to default placeholder text, your cookies won't validate properly.
Here's the fix:
Visit https://api.wordpress.org/secret-key/1.1/salt/ in your browser. WordPress.org generates a fresh set of all eight constants every time you load that page. Copy the entire output. Then open your wp-config.php file via FTP or your hosting file manager, find the existing salt block, and replace it completely.
One thing to know before you do this. Replacing the salts immediately invalidates every active login session on your site. Every admin, editor, and subscriber gets logged out. If you run a membership website, give your team a heads up first.
Took me forever to figure out why a client's multisite kept logging everyone out on a schedule. Turned out a security plugin was rotating the salts automatically every 24 hours. Aggressive, but it explained the pattern.
Fix the WordPress URL Settings
If your WordPress Address and Site Address don't match, no amount of cookie clearing will help. The cookie domain is tied to these URLs. A mismatch means the cookie is set for one domain but WordPress expects it from another.
Normally you'd fix this in Settings > General inside the WordPress dashboard. But if you're stuck in a login loop (which is the whole reason you're reading this), you can't access the dashboard. Catch-22.
Two ways around it.
Editing wp-config.php Directly
Open wp-config.php and add these two lines above the "That's all, stop editing!" comment:
define('WPHOME', 'https://yourdomain.com'); define('WPSITEURL', 'https://yourdomain.com');
Make sure both values are exactly identical. Same protocol, same www or non-www format, no trailing slash. These constants override whatever is in the database, so they take effect immediately.
This is also useful if you're running your site behind a CDN like Cloudflare and the URLs keep getting rewritten. Hardcoding them in wp-config.php removes the database as a variable. For sites that need a user friendly website experience, keeping these URLs consistent is the most basic but most overlooked step.
Updating the Database Through phpMyAdmin
If wp-config.php changes don't resolve it, the database values might be overriding things through a plugin or theme. Go directly to the source.
Log into phpMyAdmin through cPanel or your hosting control panel. Find the wpoptions table (the prefix might be different if you changed it during installation). Look for two rows:
- siteurl (optionname) should contain your exact site URL
- home (optionname) should contain the same exact URL
Edit both values to match. Save. Try logging in again.
Quick note: if you're on managed hosting like WP Engine or Kinsta, you might not have direct phpMyAdmin access. Check your host's dashboard for a database management tool, or contact support. Most managed hosts handle this kind of thing quickly since they deal with it all the time.
Check and Fix SSL Configuration
SSL problems and login issues go hand in hand. If your certificate setup is broken, WordPress authentication cookies won't work correctly because secure cookies require a valid HTTPS connection to be sent by the browser.
Start with a basic check. Open your site in a browser and click the padlock icon (or the warning triangle if something's wrong). Look for:
- Certificate expiration date. If it's expired, renew it. Let's Encrypt certificates expire every 90 days, and auto-renewal fails more often than you'd think.
- Certificate domain match. The certificate must cover the exact domain your WordPress site uses, including or excluding www.
- Mixed content warnings. Chrome DevTools (F12 > Console) will list any HTTP resources loading on an HTTPS page.
Force SSL for the admin area by adding this to wp-config.php:
define('FORCESSLADMIN', true);
This tells WordPress to always use HTTPS for wp-login.php and the entire wp-admin area. Without it, WordPress might serve the login page over HTTP on some server configurations, which means the secure authentication cookie never gets set.
About the Really Simple SSL plugin, and plugins like it. Look, they work fine for most people. But they add a layer of abstraction over something that should be handled at the server level. When these plugins break, or conflict with another plugin, your entire login flow can fall apart. Patchstack data shows that 96% of all WordPress vulnerabilities in 2024 came from plugins. If you can configure SSL through your hosting panel and .htaccess rules instead, that's one fewer plugin to worry about.
Here's a clean .htaccess redirect that forces HTTPS and prevents protocol-switching loops:
RewriteEngine On RewriteCond %{HTTPS} off RewriteRule ^(.)$ https://%{HTTPHOST}%{REQUESTURI} [L,R=301]
Place it at the top of your .htaccess file, before the WordPress rewrite block. If you're using Nginx instead of Apache, the equivalent goes in your server configuration block. Different syntax, same idea.
For any professional website, getting SSL right isn't optional. It affects authentication, search rankings, and user trust. Fixing it once at the server level saves you from chasing cookie-related login errors over and over again.
Increase the WordPress Login Cookie Lifetime
Sometimes the session expired error isn't caused by a misconfiguration. The cookie just runs out too fast.
WordPress sets login cookie duration based on whether the user checks "Remember Me" at login:
| Login Type | Cookie Duration | Behavior |
| Without "Remember Me" | 2 days | Browser session cookie; expires on close or after 48 hours. |
| With "Remember Me" | 14 days | Persistent cookie; survives browser restarts and system reboots. |
The authcookieexpiration filter controls this. You can override it in your theme's functions.php or (better) a site-specific plugin.
Here's a practical example that extends the "Remember Me" duration to 30 days:
addfilter('authcookieexpiration', function($expiration, $userid, $remember) { if ($remember) { return 30 DAYINSECONDS; } return $expiration; }, 10, 3);
The security tradeoff is real. Snicco's deep-dive into WordPress authentication found that WordPress has zero built-in protection against session hijacking via local malware on a user's device. No session rotation, no idle timeouts, no privilege-level expiration. The only thing standing between a stolen cookie and full admin access is that 2-day or 14-day window.
Setting cookies to last a year? Technically possible. But if someone grabs that cookie through XSS or a compromised browser extension, they've got a year-long key to your site. For most sites, 30 days with "Remember Me" is a reasonable middle ground.
Melapress's 2025 WordPress security survey found that 96% of respondents had experienced at least one security incident. Longer cookies expand the attack surface. Shorter cookies mean more logins. Pick your tradeoff based on who actually uses your admin panel.
Disable Plugins That Interfere With Authentication
Plugin conflicts are behind a huge number of session expired errors. The tricky part is that the plugin causing the problem is almost never the one you'd suspect.
Patchstack's 2025 report found 11,334 new vulnerabilities in the WordPress ecosystem during 2025 alone, a 42% jump over 2024. The sheer complexity of plugin interactions means authentication can break in ways nobody anticipated.
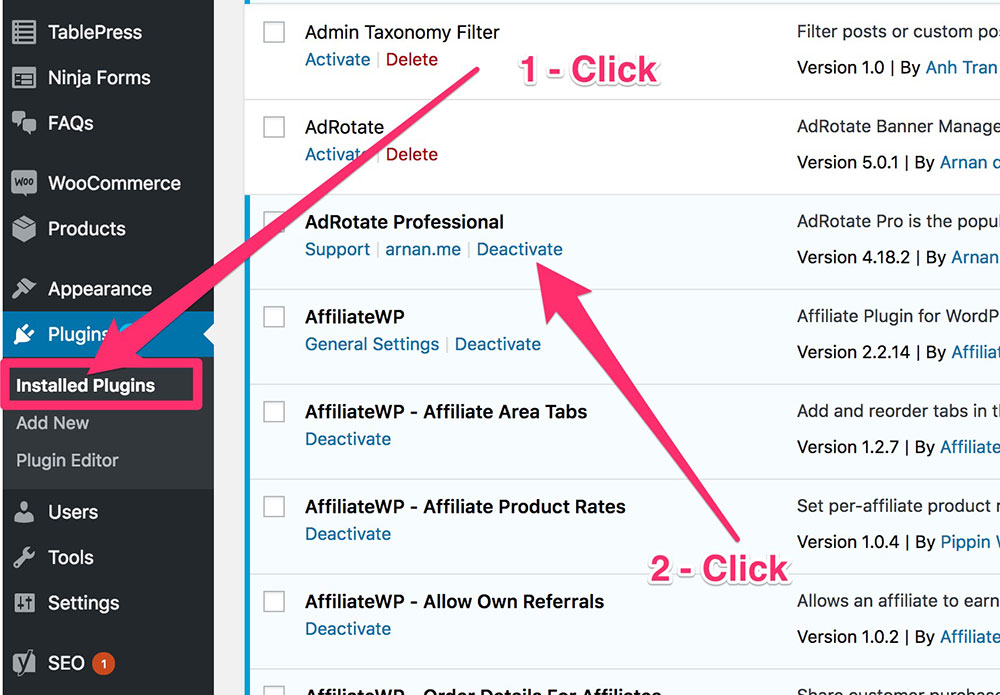
The nuclear option (and the most reliable one):
Connect to your site via FTP or your hosting file manager. Find the /wp-content/plugins/ folder. Rename it to something like plugins-disabled. Try logging in. If it works, the culprit is one of your plugins.
Rename the folder back to plugins. Then re-enable plugins one at a time through the WordPress dashboard until the error returns. That last plugin you activated? That's your problem.
The usual suspects:
- Security plugins (Wordfence, iThemes Security, All-In-One Security) that aggressively manage login sessions and cookies
- Caching plugins (W3 Total Cache, WP Super Cache, LiteSpeed Cache) that can cache the login page with stale nonce values
- Cookie consent plugins that block WordPress authentication cookies before user consent
- Two-factor authentication plugins that add extra steps conflicting with the default login flow
Digidop data shows plugin conflicts cause 65% of technical malfunctions on WordPress sites. But here's the thing. Sometimes two plugins work perfectly on their own and only break when combined. A security plugin that rotates salts plus a caching plugin that caches wp-login.php? That's a recipe for constant session timeouts.
If you find the conflicting plugin, check for updates first. The issue might already be patched. If not, look for an alternative. For sites that depend on smooth form design and login flows, one misbehaving plugin can break the entire experience.
Fix Server-Side Caching and PHP Configuration
You've checked the browser. You've checked plugins. The login still expires. At this point, the problem is almost certainly at the server level.
Server-side caching is great for performance. Terrible for login pages. When your server caches wp-login.php or wp-admin pages, it serves visitors a static HTML snapshot that includes an old nonce token. That nonce won't validate, and WordPress throws the session expired error.
Excluding Login Pages From Cache
Varnish: Add wp-login.php and /wp-admin/ to your VCL configuration's pass-through rules so they bypass the cache entirely.
Nginx FastCGI Cache: Use a fastcgicachebypass directive that checks for the wordpressloggedin cookie and skips cache when it's present.
Object cache (Redis, Memcached): These store database query results in memory. Stale session token data in the object cache can cause validation failures even when the browser cookie is correct. Flushing the object cache through your hosting panel or with wp cache flush via WP-CLI often resolves it.
If you're using Cloudflare, set a Page Rule that bypasses cache for yourdomain.com/wp-admin/ and yourdomain.com/wp-login.php. Cloudflare caching the login page is one of the most common causes of this error on sites using a CDN.
PHP Memory and Execution Limits
Low PHP memory can cause the authentication process to fail silently. The login page loads, the cookie gets set, but the server runs out of memory before completing the redirect to wp-admin.
Minimum recommended values:
memorylimit: 256M (128M is often too low for sites with multiple active plugins)maxexecutiontime: 300 seconds
You can set these in wp-config.php with define('WPMEMORYLIMIT', '256M'); or in your hosting panel's PHP settings. Some managed hosts like WP Engine and Kinsta handle this for you, but it's worth checking.
The Patchstack 2025 security report noted that hosts without application-layer security fail to block 87.8% of vulnerability exploits. If your hosting provider can't properly configure PHP and caching, the login issue is just the start of your problems. For any technology website or business running on WordPress, the server configuration matters as much as the code.
Edit the wp-login.php File as a Last Resort
If nothing else has worked, the wp-login.php file itself might be corrupted. This is rare. But it happens, and when it does, no other fix will help.
Don't edit the file. Replace it.
Go to wordpress.org/download and grab the exact version of WordPress your site is running. You can check your version in the readme.html file in your site's root directory, or in the wp-includes/version.php file. Extract the downloaded ZIP and find wp-login.php inside it. Upload that clean copy to your site's root directory via FTP, overwriting the existing one.
Check file permissions after uploading. The standard permission for wp-login.php is 644 (owner can read/write, group and others can only read). Wrong permissions can cause the server to block access or refuse to execute the file.
If you have SSH access and WP-CLI installed, run wp core verify-checksums to compare every core file against the official WordPress.org checksums. This command downloads the MD5 hashes for your exact version and flags any file that doesn't match. It's the fastest way to spot tampered or corrupted files across the entire installation.
Sucuri observed over 500,000 WordPress websites becoming infected with malware in 2024 alone. If your wp-login.php file was modified without your knowledge, the session expired error might be a symptom of something worse. A compromised core file can inject malicious redirects, steal credentials, or silently add backdoor access.
Run a malware scan. Check your error logs. And if multiple core files fail the checksum verification, consider a full reinstall of WordPress core files using wp core download --force. This replaces all core files without touching your wp-content folder, themes, plugins, or uploads.
Preventing the Session Expired Error From Returning
Fixing this error once is annoying. Fixing it repeatedly is a sign that something in your maintenance routine needs to change.
The WordPress ecosystem saw 11,334 new vulnerabilities in 2025, according to Patchstack. That's over 30 per day. Most affect plugins and themes, and many of those directly impact authentication, cookies, or session handling. Keeping things updated isn't just about new features.
Core maintenance that actually prevents this error:
- Update WordPress core, plugins, and themes as soon as stable releases drop. Patchstack found that 33% of vulnerabilities in 2024 had no patch at the time of public disclosure. The ones that do get patched need to be applied fast.
- Test updates on a staging environment before pushing to production. Especially caching and security plugins, which are the most common source of login conflicts.
- Regenerate your security salts in wp-config.php every 6 to 12 months. Think of it like changing locks after handing out too many keys.
Monitoring that catches problems early:
| What to Monitor | Tool | Why It Matters |
| SSL Certificate Expiry | UptimeRobot, Pingdom | Expired certs break login cookies and trigger browser warnings. |
| Site Uptime & Response | UptimeRobot, Jetpack | Server-side crashes or slow TTFB cause session drops and user frustration. |
| Core File Integrity | WP-CLI, Wordfence | Modified core files can corrupt authentication and allow backdoors. |
| Plugin Vulnerabilities | Patchstack, WPScan | Vulnerable plugins are the #1 attack vector for WordPress in 2026. |
| Admin Login Logs | Activity Log, Simple History | Unauthorized login attempts can be caught before a breach occurs. |
Choose a hosting provider that handles PHP session management properly and doesn't cache authenticated pages by default. Managed WordPress hosts like Kinsta, WP Engine, and Cloudways generally have these exclusions baked in. Shared hosting is hit or miss.
If you're building a new site or redesigning, following a solid website checklist that includes server configuration alongside design choices will save you from chasing down login errors months later. The session expired error is almost always a symptom of something else being slightly off. Get the foundation right, and you won't see it again.
FAQ on How To Fix The WordPress Session Expired Error
What does "your session has expired" mean in WordPress?
It means WordPress can't validate the authentication cookie stored in your browser. The cookie is either expired, corrupted, or mismatched with your site URL settings. WordPress logs you out and asks you to sign in again through wp-login.php.
Why does WordPress keep saying my session expired?
Repeated session timeouts usually point to a WordPress Address and Site Address mismatch in your settings. It can also be caused by caching plugins serving stale login pages, SSL misconfigurations, or browser extensions blocking cookies.
How do I clear cookies to fix this error?
Open your browser settings and delete cookies only for your WordPress domain. Test in an incognito window first. If the login works there, your regular browser is holding onto an old, invalid authentication cookie that needs clearing.
Will resetting WordPress security keys fix the session expired error?
Yes. Visit the WordPress.org salt generator API, copy the new keys, and paste them into wp-config.php, replacing the old ones. This invalidates all existing sessions and forces fresh cookie generation for every user.
Can caching plugins cause the session expired error?
Absolutely. Plugins like W3 Total Cache, WP Super Cache, and LiteSpeed Cache can cache wp-login.php with stale nonce values. Exclude the login page and wp-admin from your caching rules to fix it.
Does SSL affect WordPress login cookies?
Yes. If your SSL certificate is expired or your site mixes HTTP and HTTPS, the browser may block secure authentication cookies. Set FORCESSLADMIN to true in wp-config.php and confirm your certificate covers your exact domain.
How do I fix the session expired error without dashboard access?
Use FTP or your hosting file manager to edit wp-config.php. Add WPHOME and WPSITEURL constants with your correct site URL. You can also rename the plugins folder to disable all plugins and regain login access.
Can a security plugin cause this error?
Yes. Plugins like Wordfence and iThemes Security sometimes manage login sessions aggressively. They may rotate salts, enforce short cookie lifetimes, or block authentication cookies. Temporarily disable the plugin via FTP to test.
How do I increase the WordPress login cookie lifetime?
Use the authcookieexpiration filter in functions.php or a site-specific plugin. The default is 2 days without "Remember Me" and 14 days with it. You can extend this, but longer durations increase session hijacking risk.
How do I check if wp-login.php is corrupted?
Run wp core verify-checksums through WP-CLI to compare your files against official WordPress.org hashes. If wp-login.php fails the check, download a fresh copy from wordpress.org matching your exact version and replace it via FTP.
Conclusion
Knowing how to fix the WordPress session expired error saves you from one of the most frustrating wp-admin login problems out there. The fix is almost never complicated. It just requires checking the right thing in the right order.
Start with browser cookies and work your way up. Check your WordPress URL settings in the database. Verify your SSL certificate. Regenerate the salt keys in wp-config.php if needed.
If those don't solve it, look at plugin conflicts and server-side caching rules. Security plugins and object cache setups like Redis or Memcached are common culprits that most people overlook.
Run wp core verify-checksums` through WP-CLI periodically. Keep plugins updated. Monitor your SSL expiry dates with tools like Uptime Robot. These small habits prevent the error from coming back.
The session expired error is a symptom. Fix the root cause, and your WordPress dashboard stays ac